異常檢測(cè)技術(shù)已經(jīng)被應(yīng)用于確保解決網(wǎng)絡(luò)安全和網(wǎng)聯(lián)車輛安全性等挑戰(zhàn)性問題。本文提出了這個(gè)領(lǐng)域的先前研究的分類。本文提出的分類學(xué)有3個(gè)總體維度,包括9個(gè)類別和38個(gè)子類別。從調(diào)查中得出的主要觀察結(jié)果是:真實(shí)世界的數(shù)據(jù)集很少被使用,大多數(shù)結(jié)果來(lái)自仿真;V2V / V2I通信和車載通信不一起考慮;提議的技術(shù)很少針對(duì)基線進(jìn)行評(píng)估;網(wǎng)聯(lián)車輛的安全沒有網(wǎng)絡(luò)安全那么受關(guān)注。
I.介紹
Velosa等人 [1]預(yù)測(cè)到2020年將有25億輛網(wǎng)聯(lián)車輛上路。車聯(lián)網(wǎng)是指能夠連接到網(wǎng)絡(luò)的車輛,即它可以與其他車輛(V2V)或基礎(chǔ)設(shè)施(V2I)進(jìn)行通信,因而可以增強(qiáng)信息娛樂功能以及可以減少碰撞和避免擁塞[2]復(fù)雜的等進(jìn)行復(fù)雜功能的應(yīng)用。在V2V的情況下,通常建議車輛之間形成車輛自組織網(wǎng)絡(luò)( VANET )。
雖然網(wǎng)聯(lián)車輛可以增加乘客的便利性以及行駛的安全性,但它們也很容易受到網(wǎng)絡(luò)攻擊[3]。一些研究[4]、[5]、[6]已經(jīng)發(fā)現(xiàn)并證明了普通車輛中可利用的漏洞。網(wǎng)聯(lián)車輛連接數(shù)量的增加會(huì)增加這些漏洞的脆弱性的影響和普遍程度。此外,確保網(wǎng)聯(lián)車輛的安全性變得至關(guān)重要,因此各國(guó)政府加大了實(shí)現(xiàn)功能性VANET的力度[7]。
本文對(duì)自2000年初以來(lái)的研究進(jìn)行了調(diào)查和分析,即對(duì)網(wǎng)聯(lián)車輛的安全和網(wǎng)絡(luò)安全問題進(jìn)行異常檢測(cè)。異常檢測(cè)是識(shí)別不遵循預(yù)期模式[ 8 ]的數(shù)據(jù)點(diǎn)或事件的過程。據(jù)悉,這是第一項(xiàng)在此背景下調(diào)查異常檢測(cè)使用的研究。我們提出了一個(gè)基于3個(gè)總體類別和9個(gè)子類別的分類法。我們還有38個(gè)維度來(lái)分類所有的調(diào)查論文。
我們調(diào)查和分析后得出以下推論:
1)大多數(shù)研究(65篇調(diào)查論文中有37篇)是在仿真數(shù)據(jù)集上進(jìn)行的(65篇調(diào)查論文中只有19篇使用了真實(shí)世界的數(shù)據(jù)集)。
2)V2X和車載通信基本上沒有被一起探索(65個(gè)調(diào)查論文中的1個(gè)除外),這使得研究比較分散。
3)與網(wǎng)絡(luò)安全相比,網(wǎng)聯(lián)車輛的安全性(65份調(diào)查論文中只有21份)的研究較少。
4)與基線相比,新提出的采用異常檢測(cè)技術(shù)的方法很少(在65份調(diào)查論文中只有4篇),導(dǎo)致我們提出的方法的有效性量化較差。
因此,我們建議,應(yīng)該更加重視建立基準(zhǔn)和基線技術(shù),以此來(lái)評(píng)估新技術(shù)。此外,我們還主張更多地利用真實(shí)世界的數(shù)據(jù),而不是仿真數(shù)據(jù)。
論文的其余部分組織如下:我們?cè)诘贗I部分和第III部分探討相關(guān)工作和我們的調(diào)查方法,并在第Ⅳ部分提出我們的分類法。
II.相關(guān)工作
與當(dāng)前的調(diào)查不同,自20世紀(jì)初以來(lái),以前的調(diào)查分別考慮了VANET和車載網(wǎng)絡(luò)。例如,outernali等人[ 9 ]調(diào)查了VANETs以及Sakiz等人提出的各種入侵檢測(cè)方法。[10]全面調(diào)查了所有可能的攻擊,并提出了與VANETs相關(guān)的檢測(cè)機(jī)制。這兩項(xiàng)研究都沒有考慮可能的基于車載網(wǎng)絡(luò)的網(wǎng)絡(luò)安全問題。很少有研究調(diào)查車載網(wǎng)絡(luò)中可能存在的威脅和對(duì)策。例如Liu等人、McCune等人和Kelberger等人 [11],[12],[13]提出了車載(控制器局域網(wǎng)(CAN),本地互連網(wǎng)絡(luò)(LIN),F(xiàn)lexRay等)的各種威脅和可能的對(duì)策,網(wǎng)絡(luò)安全問題(基于VANET的問題不是考慮)。我們目前的調(diào)查是第一次在網(wǎng)聯(lián)車輛的背景下審查異常檢測(cè)技術(shù)。
III.調(diào)查方法
為了確保可重復(fù)性,我們的調(diào)查遵循Wholin的滾雪球方法[14]如下。
范圍定義:繼Chandola等人之后。 [8]我們將異常檢測(cè)定義為“在不符合預(yù)期行為的數(shù)據(jù)中查找模式”。形成或?qū)W習(xí)模型,然后監(jiān)測(cè)數(shù)據(jù)的一致性。
收集初步研究:我們?cè)贕oogle學(xué)術(shù)中通過關(guān)鍵字搜索確定了一組初始論文。我們這樣做是為了避免出版商的偏見。使用的關(guān)鍵詞是: "異常檢測(cè)"、"連接車輛"、" VANET "、" V2I "、" V2V "、"入侵檢測(cè)"、"不當(dāng)行為檢測(cè)"、" CAN總線"、"車內(nèi)"、"安全"、"安保"。
滾雪球:通過關(guān)鍵詞搜索收集的初始集可能并不詳盡。因此,我們進(jìn)行了前后滾雪球式的收集,以收集初始集引用的所有參考文獻(xiàn)。然后通過閱讀摘要包括或排除論文,然后考慮范圍的徹底閱讀(從而消除超出我們范圍的論文)。這個(gè)滾雪球過程被重復(fù)進(jìn)行,直到?jīng)]有新的相關(guān)論文被添加。我們最終研究了有65篇論文。
雖然Wholin [14]建議聯(lián)系該領(lǐng)域的知名研究人員以獲取更多相關(guān)文獻(xiàn),但我們忽略了這一步驟,因?yàn)殍b于該領(lǐng)域的多樣性,我們無(wú)法最終確定最重要的研究人員。
數(shù)據(jù)提取和分類發(fā)展:通過Wholin的調(diào)查方法[14],一旦詳盡地收集了所有相關(guān)論文,我們就記下了每篇論文的關(guān)鍵要素。我們使用了一種開放式卡片分類技術(shù)[15],收集了關(guān)鍵點(diǎn),以得出我們提議的分類的維度。開放式卡片分類技術(shù)是通過參與者之間的共識(shí)將關(guān)鍵元素組織成概念組的過程。我們使用這種技術(shù)來(lái)達(dá)到我們的38個(gè)維度(底層)。然后,我們使用自下而上的方法,將這些維度分為9個(gè)子類別(中級(jí)),我們后來(lái)根據(jù)排序的多次迭代將其歸入3個(gè)總體類別(頂級(jí))。我們只在這項(xiàng)研究的作者中進(jìn)行了公開卡片分類的過程,盡管這個(gè)過程通常涉及更大的群體[ 15 ]。最后,我們通過標(biāo)記將收集到的每篇論文都?xì)w入我們的分類體系,通過用它們占據(jù)的每個(gè)指定維度標(biāo)記每個(gè)論文。
IV.分類
上述過程產(chǎn)生了一個(gè)分類法(見圖1),包含3個(gè)頂級(jí)類別,9個(gè)子類別和38個(gè)維度。這些類別代表了研究領(lǐng)域的更高層次特征。我們的目標(biāo)是確定每篇論文所針對(duì)的威脅、解決方案和研究特征。特別是,抓住了研究特點(diǎn),對(duì)實(shí)驗(yàn)的類型和嚴(yán)謹(jǐn)性進(jìn)行了闡述。
反過來(lái),每個(gè)提議的類別包括幾個(gè)子類別。威脅特征有兩個(gè)子類別,解決方案特征有4個(gè)子類別,研究特征各有3個(gè)子類別,可以更好地捕捉每個(gè)類別的特征。子類別還具有如圖1所示的尺寸,這些尺寸捕捉并突出了區(qū)分每個(gè)子類別的技術(shù)差異,如下所示:
A.威脅特征
這一類別涉及每篇調(diào)查論文所涉及的威脅。我們將其劃分為兩個(gè)正交的子類別,如下所示。
1)攻擊面:攻擊面識(shí)別網(wǎng)聯(lián)車輛中的潛在弱點(diǎn)。例如,一篇論文可能是針對(duì)基于CAN總線的攻擊(其他總線由于缺乏足夠的文獻(xiàn)而未被考慮),而其他一些論文則專門關(guān)注偽造車輛ECU(電子控制單元)輸出的攻擊。
2)攻擊方法:一篇論文可能涉及不止一種攻擊方法。我們特別提請(qǐng)注意此子類別中的黑/灰/蟲洞攻擊維度。這些是基于路由的攻擊,包括丟棄、選擇性轉(zhuǎn)發(fā)或惡意重新路由VANET[16]中的通信數(shù)據(jù)包。
B.解決方案特征
這一類別代表了為應(yīng)對(duì)威脅而提議的解決方案的性質(zhì)。
1)動(dòng)機(jī):異常檢測(cè)技術(shù)是用于檢測(cè)威脅還是也提供對(duì)威脅的響應(yīng)?
2)部署點(diǎn):網(wǎng)聯(lián)車輛的哪一部分是建議部署的解決方案。例如,可以在車輛的ECU中或在VANET的中央管理機(jī)構(gòu)(CA)或路側(cè)單元(RSU)中部署解決方案。
3)安全目標(biāo):是否保護(hù)了信息安全(完整性,機(jī)密性,可用性)[17]和/或網(wǎng)聯(lián)車輛的安全性。人身安全不在這項(xiàng)工作的范圍之內(nèi)。
4)異常檢測(cè)方法:異常可以用多種方式檢測(cè)。分類法區(qū)分了所使用的異常檢測(cè)方法。我們?cè)谶@里提請(qǐng)注意基于規(guī)則的方法維度,它只代表從車輛操作中自動(dòng)推斷規(guī)則的研究,而不是那些從專家那里引出規(guī)則的研究。
C.研究特點(diǎn)
雖然上述類別根據(jù)已解決的威脅和已確定的維度區(qū)分了先前的研究,但這一類別涉及研究方法和數(shù)據(jù)。
1)科學(xué)性:該子類別可記錄一篇論文是屬于理論論文,實(shí)驗(yàn)論文,實(shí)證論文還是調(diào)查論文。論文可以是類型的組合。
2)數(shù)據(jù)來(lái)源:該子類別記錄論文是否使用現(xiàn)實(shí)數(shù)據(jù)或仿真數(shù)據(jù)。
3)數(shù)據(jù)集:該子類別記錄論文是使用VANET還是車載(CAN總線等)或自然數(shù)據(jù)[18]。如果一篇論文觀察了運(yùn)行中的連接車輛,并觀察了其自然運(yùn)行環(huán)境中的數(shù)據(jù),而沒有引入任何人工數(shù)據(jù)(例如,攻擊),則認(rèn)為該論文使用了自然數(shù)據(jù)。
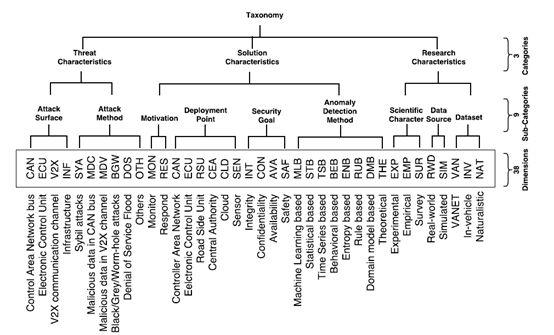
圖1.描述所有維度、類別、子類別的分類結(jié)構(gòu)。框中的尺寸首字母縮略詞是表I的列標(biāo)題
V.從分類法中得出的推論
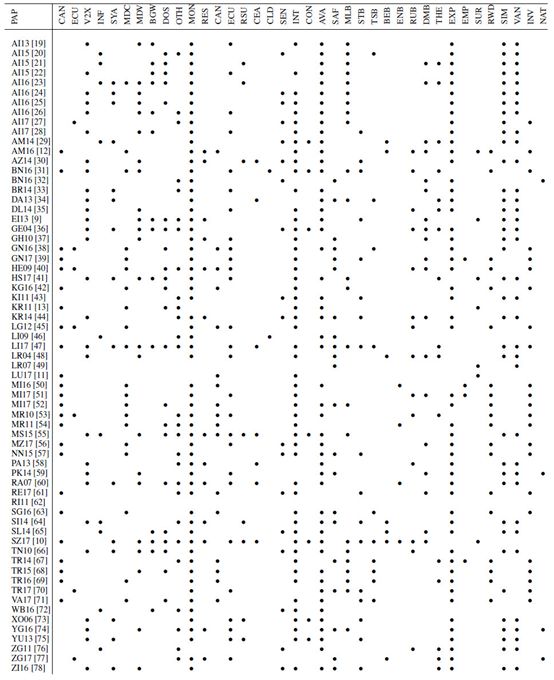
表I列出了根據(jù)第IV節(jié)中描述的分類法對(duì)第III部分收集的論文進(jìn)行的分類。以這種方式呈現(xiàn)論文分類的主要目的是從中得出推論和見解,在本文中,我們得出的推論側(cè)重于分析研究現(xiàn)狀。表I中的每篇論文在“PAP”欄中用第一個(gè)字母和最后一個(gè)字母表示第一作者的姓氏和出版年份。
A.關(guān)注
我們對(duì)調(diào)查的分析中發(fā)現(xiàn)了兩個(gè)問題。研究VANET的論文都沒有使用真實(shí)世界的數(shù)據(jù)。在我們調(diào)查和分類的所有論文中,VANET中甚至沒有一篇論文(在研究VANET數(shù)據(jù)的35/65篇論文中)使用真實(shí)數(shù)據(jù)(所有研究都是在仿真數(shù)據(jù)集上進(jìn)行的(37/65篇論文))。我們可以從表I中看到這一點(diǎn),觀察到在研究特征類別中沒有VANET和真實(shí)世界維度上都有標(biāo)記的論文。總體而言,在65篇被調(diào)查的論文中,只有28篇使用真實(shí)世界的數(shù)據(jù)集(大部分在車載網(wǎng)絡(luò)研究中)。
我們所提出的基于異常檢測(cè)的解決方案很少針對(duì)基線進(jìn)行評(píng)估。從表I中的經(jīng)驗(yàn)維度(EMP)可以看出,只有4篇被調(diào)查的論文(65篇調(diào)查論文中有4篇)評(píng)估了針對(duì)基線的擬議解決方案。我們預(yù)計(jì)建立一個(gè)量化改進(jìn)的基線將是一個(gè)領(lǐng)域成熟的可喜跡象[79]。
B.差距
這個(gè)研究領(lǐng)域還有三個(gè)明顯的空白有待填補(bǔ)。
除了65篇調(diào)查論文中的1篇論文(Levi等[47])外,沒有其他論文通過同時(shí)分析車載和VANET數(shù)據(jù)來(lái)考慮保護(hù)網(wǎng)聯(lián)車輛:即使來(lái)自VANET或車載網(wǎng)絡(luò)的故障/惡意通信也可能影響網(wǎng)聯(lián)車輛的安全性。例如,如果網(wǎng)聯(lián)車輛的車載網(wǎng)絡(luò)受到危害,則可能開始將故障數(shù)據(jù)發(fā)送到VANET,而VANET又可能危及其他車輛。
與確保網(wǎng)絡(luò)安全相比,車聯(lián)網(wǎng)安全性受到的關(guān)注較少。在許多情況下,安全漏洞可能危及網(wǎng)聯(lián)車輛的安全性,反之亦然。因此,即使在沒有安全問題的情況下也確保網(wǎng)聯(lián)車輛的安全性是重要的。只有少數(shù)被調(diào)查的論文(65篇被調(diào)查論文中的13篇)也考慮應(yīng)對(duì)已發(fā)現(xiàn)的威脅。大多數(shù)論文(65篇調(diào)查論文中的59篇)僅用于在異常檢測(cè)的幫助下監(jiān)測(cè)威脅。
表Ⅰ
顯示分類論文分配的矩陣
VI.結(jié)論
為了提高連接車輛的安全性,本文對(duì)異常檢測(cè)進(jìn)行了研究。異常檢測(cè)研究的廣泛使用和零散的發(fā)表導(dǎo)致了大量文獻(xiàn)的出現(xiàn),其中存在許多空白和問題。為了找出這些差距和關(guān)注點(diǎn),并對(duì)研究領(lǐng)域做了一個(gè)全面的了解,我們對(duì)65份相關(guān)論文進(jìn)行了調(diào)查,在調(diào)查期間開發(fā)了一種新的分類法,并根據(jù)分類法對(duì)調(diào)查的論文進(jìn)行了分類,以找出差距。
該調(diào)查表明:
大部分研究是在仿真數(shù)據(jù)上進(jìn)行的(65份調(diào)查論文中有37篇);車載網(wǎng)絡(luò)數(shù)據(jù)和VANET數(shù)據(jù)很少被一起考慮來(lái)用于保護(hù)網(wǎng)聯(lián)車輛(65份調(diào)查論文中除1份外);
網(wǎng)聯(lián)車輛安全研究沒有得到網(wǎng)絡(luò)安全研究那么多關(guān)注(在65篇調(diào)查論文中只有13篇);
而且,許多研究沒有對(duì)照基線評(píng)估提出新的技術(shù)(在65篇調(diào)查論文中只有4篇這樣做),這可能導(dǎo)致難以量化的結(jié)果。
因此,我們敦促研究人員解決這些發(fā)現(xiàn)的問題,并定期用我們提議的分類學(xué)來(lái)分析研究,以了解研究的現(xiàn)狀及其演變。
REFERENCES
[1] A. Velosa, J. Hines, H. LeHong, and E.Perkins, “Predicts 2015: TheInternet of Things,” Gartner: Stamford, CT, USA,2014.
[2] C. Evans-Pughe, “The connected car,” IEEReview, vol. 51, no. 1, pp.42–46, 2005.
[3] P. Papadimitratos, L. Buttyan, T. Holczer,E. Schoch, J. Freudiger,M. Raya, Z. Ma, F. Kargl, A. Kung, and J.-P. Hubaux,“Securevehicular communication systems: design and architecture,” IEEE
Communications Magazine, vol. 46, no. 11,2008.
[4] S. Checkoway, D. McCoy, B. Kantor, D.Anderson, H. Shacham,S. Savage, K. Koscher, A. Czeskis, F. Roesner, T. Kohno etal.,“Comprehensive experimental analyses of automotive attack surfaces.”
in USENIX Security Symposium. SanFrancisco, 2011.
[5] C. Miller and C. Valasek, “Adventuresin automotive networks andcontrol units,” DEF CON, vol. 21, pp. 260–264, 2013.
[6] R. M. Ishtiaq Roufa, H. Mustafaa, S. O.Travis Taylora, W. Xua,M. Gruteserb, W. Trappeb, and I. Seskarb, “Security andprivacy vulnerabilities of in-car wireless networks: A tire pressure monitoringsystem case study,” in 19th USENIX Security Symposium, Washington DC, 2010, pp.11–13.
[7] U. DoT, “Connected vehicle pilotdeployment program,” 2016. [Online]. Available:https://www.its.dot.gov/pilots/index.htm
[8] V. Chandola, A. Banerjee, and V. Kumar,“Anomaly detection: A survey,” ACM computing surveys (CSUR), vol. 41, no. 3, p.15, 2009.
[9] M. Erritali and B. E. Ouahidi, “Areview and classification of various VANET intrusion detection systems,” in2013 National Security Days (JNS3), 2013, pp. 1–6.
[10] F. Sakiz and S. Sen, “A survey of attacksand detection mechanisms on intelligent transportation systems: VANETs andIoV,” Ad Hoc Networks, vol. 61, pp. 33–50, 2017.
[11] J. Liu, S. Zhang, W. Sun, and Y. Shi, “In-vehiclenetwork attacks and countermeasures: challenges and future directions,” IEEENetwork, vol. 31, no. 5, pp. 50–58, 2017.
[12] S. Abbott-McCune and L. A. Shay,“Intrusion prevention system of automotive network CAN bus,” in 2016 IEEEInternational Carnahan Conference on Security Technology (ICCST), 2016, pp.1–8.
[13] P. Kleberger, T. Olovsson, and E. Jonsson,“Security aspects of the in-vehicle network in the connected car,” in 2011 IEEEIntelligent Vehicles Symposium (IV), 2011, pp. 528–533.
[14] C. Wohlin, “Guidelines for snowballingin systematic literature studies and a replication in software engineering,” inProc. 18th Intl. Conf. on Evaluation and Assessment in Software Engineering,2014, p. 38.
[15] M. Soegaard and R. F. Dam, Theencyclopedia of human-computer interaction. The Interaction Design Foundation,2012, ch. 2.2: Card Sorting.
[16] V. S. Abel, “Survey of attacks on mobileadhoc wireless networks,” International Journal on Computer Science andEngineering, vol. 3, no. 2, pp. 826–829, 2011.
[17] J. Andress, The basics of informationsecurity: understanding the fundamentals of InfoSec in theory and practice.Syngress, 2014.
[18] T. A. Dingus, S. G. Klauer, V. L.Neale, A. Petersen, S. E. Lee, J. Sudweeks, M. Perez, J. Hankey, D. Ramsey, S.Gupta et al., “The 100-car naturalistic driving study, phase II-results of the100-car field experiment,” U.S DoT, Tech. Rep., 2006.
[19] K. M. Alheeti, L. Al-Jobouri, and K. McDonald-Maier,“Increasing the rate of intrusion detection based on a hybrid technique,” in2013 5th Computer Science and Electronic Engineering Conference(CEEC). IEEE, 2013, pp. 179–182.
[20] K. M. Alheeti, A. Gruebler, and K.McDonald-Maier, “An intrusion detection system against malicious attacks on thecommunication network of driverless cars,” in 2015 12th Annual IEEE Consumer Communicationsand Networking Conf. (CCNC), 2015, pp. 916–921.
[21] K. M. Alheeti, A. Gruebler, and K. McDonald-Maier,“On the detection of grey hole and rushing attacks in self-driving vehicular networks,”in 2015 7th Computer Science and Electronic Engineering Conference (CEEC).IEEE, 2015, pp. 231–236.
[22] K. M. Alheeti, A. Gruebler, and K.McDonald-Maier, “An intrusion detection system against black hole attacks onthe communication network of self-driving cars,” in 2015 6th InternationalConference on Emerging Security Technologies (EST). IEEE, 2015, pp. 86–91.
[23] K. M. Alheeti and K. McDonald-Maier,“Hybrid intrusion detection in connected self-driving vehicles,” in 22nd IEEEInternational Conference on Automation and Computing (ICAC), 2016, pp. 456–461.
[24] K. M. Alheeti and K. McDonald-Maier,“An intelligent intrusion detection scheme for self-driving vehicles based onmagnetometer sensors,” in 2016 International Conference for Students on AppliedEngineering (ICSAE). IEEE, 2016, pp. 75–78.
[25] K. M. Alheeti, A. Gruebler, K.McDonald-Maier, and A. Fernando, “Prediction of DoS attacks in external communication for self-drivingvehicles using a fuzzy Petri net model,” in 2016 IEEE International Conferenceon Consumer Electronics (ICCE), 2016, pp. 502–503.
[26] K. M. Alheeti, A. Gruebler, and K.McDonald-Maier, “Intelligent intrusion detection of grey hole and rushingattacks in self-driving vehicular networks,” Computers, vol. 5, no. 3, p. 16,2016.
[27] K. M. Alheeti, R. Al-Zaidi, J. Woods,and K. McDonald-Maier, “An intrusion detection scheme for driverless vehiclesbased gyroscope sensor profiling,” in 2017 IEEE International Conference onConsumer Electronics (ICCE), 2017, pp. 448–449.
[28] K. M. Alheeti, A. Gruebler, and K.McDonald-Maier, “Using discriminant analysis to detect intrusions in externalcommunication for self-driving vehicles,” Digital Communications and Networks,vol. 3, no. 3, pp. 180–187, 2017.
[29] M. Al-Mutaz, L. Malott, and S. Chellappan,“Detecting Sybil attacks in vehicular networks,” Journal of Trust Management,vol. 1, p. 4, 2014.
[30] K. C. Abdelaziz, N. Lagraa, and A.Lakas, “Trust model with delayed verification for message relay in VANETs,” in2014 International Wireless Communications and Mobile Computing Conference (IWCMC).IEEE, 2014, pp. 700–705.
[31] O. Berlin, A. Held, M. Matousek, and F.Kargl, “POSTER: Anomalybased misbehaviour detection in connected car backends,”in 2016 IEEE Vehicular Networking Conference (VNC), 2016, pp. 1–2.
[32] A. R. Beukman, G. P. Hancke, and B. J.Silva, “A multi-sensor system for detection of driver fatigue,” in 14thInternational Conference on Industrial Informatics (INDIN). IEEE, 2016, pp.870–873.
[33] N. Bissmeyer, “Misbehavior detectionand attacker identification in vehicular ad-hoc networks,” PhD Thesis, TUBerlin, 2014.
[34] N. Dutta and S. Chellappan, “A time-seriesclustering approach for Sybil attack detection in vehicular ad hoc networks,”in Proc. Intl. Conf. on Advances in Vehicular Systems, Technologies, andApplications, Nice, 2013, pp. 21–26.
[35] S. Dietzel, R. van der Heijden, H. Decke,and F. Kargl, “A flexible, subjective logic-based framework for misbehaviordetection in V2V networks,” in Proceeding of IEEE International Symposium on aWorld of Wireless, Mobile and Multimedia Networks 2014, 2014, pp. 1–6.
[36] P. Golle, D. Greene, and J. Staddon,“Detecting and correcting malicious data in VANETs,” in Proceedings of the 1stACM International Workshop on Vehicular Ad Hoc Networks. ACM, 2004, pp. 29–37.
[37] M. Ghosh, A. Varghese, A. Gupta, A. A.Kherani, and S. N. Muthaiah, “Detecting misbehaviors in VANET with integrated root-cause analysis,”Ad Hoc Networks, vol. 8, no. 7, pp. 778–790, 2010.
[38] M. Gmiden, M. H. Gmiden, and H.Trabelsi, “An intrusion detection method for securing in-vehicle CAN bus,” in2016 17th International Conference on Sciences and Techniques of AutomaticControl and Computer Engineering (STA). IEEE, 2016, pp. 176–180.
[39] A. Ganesan, J. Rao, and K. Shin,“Exploiting consistency among heterogeneous sensors for vehicle anomalydetection,” SAE, Tech. Rep. 2017-01-1654, 2017.
[40] T. Hoppe, S. Kiltz, and J. Dittmann,“Applying intrusion detection to automotive it-early insights and remainingchallenges,” vol. 4, pp. 226–235, Jan. 2009.
[41] R. E. Haas, D. P. F. Mller, P. Bansal,R. Ghosh, and S. S. Bhat, “Intrusion detection in connected cars,” in 2017 IEEE Intl. Conf. on ElectroInformation Technology (EIT), 2017, pp. 516–519.
[42] M.-J. Kang and J.-W. Kang, “Intrusiondetection system using deep neural network for in-vehicle network security,”PLoS ONE, vol. 11, no. 6, 2016.
[43] B. Khorashadi, F. Liu, D. Ghosal, M.Zhang, and C. N. Chuah, “Distributed automated incident detection with VGRID,”IEEE Wireless Communications, vol. 18, no. 1, pp. 64–73, 2011.
[44] N. Kumar and N. Chilamkurti, “Collaborativetrust aware intelligent intrusion detection in VANETs,” Computers &Electrical Engineering, vol. 40, no. 6, pp. 1981–1996, 2014.
[45] C. Ling and D. Feng, “An algorithm fordetection of malicious messages on CAN buses,” in 2012 National Conference onInformation Technology and Computer Science. Atlantis Press, 2012.
[46] X. Li, Z. Li, J. Han, and J. G. Lee,“Temporal outlier detection in vehicle traffic data,” in 2009 IEEE 25thInternational Conference on Data Engineering, 2009, pp. 1319–1322.
[47] M. Levi, Y. Allouche, and A. Kontorovich,“Advanced analytics for connected cars cyber security,” arXiv:1711.01939 [cs],2017.
[48] T. Leinm¨uller, A. Held, G. Sch¨afer,and A. Wolisz, “Intrusion detection in VANETs,” in In Proceedings of 12th IEEEInternational Conference on Network Protocols (ICNP 2004) Student PosterSession, 2004.
[49] T. Leinm¨uller, E. Schoch, and C.Maihofer, “Security requirements and solution concepts in vehicular ad hoc networks,”in 4th IEEE Conf. on Wireless on Demand Network Systems and Services, 2007, pp.84–91.
[50] M. Marchetti, D. Stabili, A. Guido,and M. Colajanni, “Evaluation of anomaly detection for in-vehicle networksthrough informationtheoretic algorithms,” in 2016 IEEE 2nd International Forumon Research and Technologies for Society and Industry Leveraging a BetterTomorrow (RTSI), 2016, pp. 1–6.
[51] M. Marchetti and D. Stabili, “Anomalydetection of CAN bus messages through analysis of ID sequences,” in IntelligentVehicles Symposium (IV), 2017 IEEE. IEEE, 2017, pp. 1577–1583.
[52] F. Martinelli, F. Mercaldo, V. Nardone,and A. Santone, “Car hacking identification through fuzzy logic algorithms,” in2017 IEEE International Conference on Fuzzy Systems (FUZZ-IEEE), 2017, pp. 1–7.
[53] M. M¨uter, A. Groll, and F. C. Freiling,“A structured approach to anomaly detection for in-vehicle networks,” in 20106th International Conference on Information Assurance and Security, 2010, pp.92–98.
[54] M. M¨uter and N. Asaj, “Entropy-based anomalydetection for invehicle networks,” in 2011 IEEE Intelligent Vehicles Symposium(IV), 2011, pp. 1110–1115.
[55] L. Maglaras, “A novel distributedintrusion detection system for vehicular ad hoc networks,” InternationalJournal of Advanced Computer Science and Applications(IJACSA), vol. 6, 2015.
[56] M. Markovitz and A. Wool, “Fieldclassification, modeling and anomaly detection in unknown CAN bus networks,”Vehicular Communications, vol. 9, pp. 43–52, 2017.
[57] S. N. Narayanan, S. Mittal, and A. Joshi,“Using data analytics to detect anomalous states in vehicles,” arXiv:1512.08048[cs], 2015.
[58] V. L. Praba and A. Ranichitra, “Detectingmalicious vehicles and regulating traffic in VANET using RAODV protocol,”International Journal of Computer Applications, vol. 84, no. 1, 2013.
[59] O. Pattnaik and B. K. Pattanayak,“Security in vehicular ad hoc network based on intrusion detection system,”American Journal of Applied Sciences, vol. 11, no. 2, pp. 337–346, 2014.
[60] M. Raya, P. Papadimitratos, I. Aad, D.Jungels, and J. p Hubaux, “Eviction of misbehaving and faulty nodes in vehicular networks,” IEEEJournal on Selected Areas in Communications, vol. 25, no. 8, pp. 1557–1568,2007.
[61] R. Rieke, M. Seidemann, E. K. Talla,D. Zelle, and B. Seeger, “Behavior analysis for safety and security inautomotive systems,” in 2017 25th Euromicro International Conference on Parallel,Distributed and Network-Based Processing (PDP), 2017, pp. 381–385.
[62] J. Rezgui and S. Cherkaoui, “Detectingfaulty and malicious vehicles using rule-based communications data mining,” in2011 IEEE 36th Conference on Local Computer Networks, 2011, pp.827–834.
[63] H. M. Song, H. R. Kim, and H. K. Kim,“Intrusion detection system based on the analysis of time intervals of CANmessages for invehicle network,” in 2016 International Conference onInformation Networking (ICOIN). IEEE, 2016, pp. 63–68.
[64] H. Sedjelmaci, T. Bouali, and S. M.Senouci, “Detection and prevention from misbehaving intruders in vehicularnetworks,” in 2014 IEEE Global Communications Conference, 2014, pp. 39–44.
[65] H. Sedjelmaci and S. M. Senouci, “A newintrusion detection framework for vehicular networks,” in 2014 IEEEInternational Conference on Communications (ICC), 2014, pp. 538–543.
[66] D. Tian, Y. Wang, G. Lu, and G. Yu, “Avehicular ad hoc networks intrusion detection system based on BUSNet,” in 20102nd International Conference on Future Computer and Communication, vol. 1. IEEE,2010, pp. V1–225–V1–229.
[67] A. Theissler, “Anomaly detection inrecordings from in-vehicle networks,” Big data and applications, p. 23, 2014.
[68] A. Taylor, N. Japkowicz, and S. Leblanc,“Frequency-based anomaly detection for the automotive CAN bus,” in 2015 IEEEWorld Congress on Industrial Control Systems Security (WCICSS), 2015, pp.45–49.
[69] A. Taylor, S. Leblanc, and N.Japkowicz, “Anomaly detection in automobile control network data with longshort-term memory networks,” in 2016 IEEE International Conference on DataScience and Advanced Analytics (DSAA), 2016, pp. 130–139.
[70] A. Theissler, “Detecting known andunknown faults in automotive systems using ensemble-based anomaly detection,”Knowledge-Based Systems, vol. 123, pp. 163–173, 2017.
[71] D. K. Vasistha, “Detecting anomaliesin controller area network for automobiles,” Ph.D. dissertation, Texas A&MUniversity, 2017.
[72] O. A. Wahab, A. Mourad, H. Otrok, andJ. Bentahar, “CEAP: SVMbased intelligent detection model for clusteredvehicular ad hoc networks,” Expert Systems with Applications, vol. 50, pp.40–54, 2016.
[73] B. Xiao, B. Yu, and C. Gao, “Detectionand localization of Sybil nodes in VANETs,” in Proceedings of the 2006 Workshopon Dependability Issues in Wireless Ad Hoc Networks and Sensor Networks. ACM, 2006,pp. 1–8.
[74] S. Yang, Z. Liu, J. Li, S. Wang, andF. Yang, “Anomaly detection for Internet of Vehicles: A trust management schemewith affinity propagation,” Mobile Information Systems, vol. 2016, pp. 1–10,2016.
[75] B. Yu, C.-Z. Xu, and B. Xiao, “DetectingSybil attacks in VANETs,” Journal of Parallel and Distributed Computing, vol.73, no. 6, pp. 746–756, 2013.
[76] Y. Zhang and G. Cao, “V-PADA: Vehicle-platoon-awaredata access in VANETs,” IEEE Transactions on Vehicular Technology, vol. 60, no.5, pp. 2326–2339, 2011.
[77] M. Zhang, C. Chen, T. Wo, T. Xie, M.Z. A. Bhuiyan, and X. Lin, “SafeDrive: online driving anomaly detection from large-scale vehicledata,” IEEE Transactions on Industrial Informatics, vol. 13, no. 4, pp. 2087–2096,2017.
[78] K. Zaidi, M. B. Milojevic, V.Rakocevic, A. Nallanathan, and M. Rajarajan, “Host-based intrusiondetection for vanets: A statistical approach to rogue node detection,” IEEETransactions on Vehicular Technology, vol. 65, no. 8, pp. 6703–6714, 2016.
[79]S. Lessmann, B. Baesens, C. Mues, and S. Pietsch, “Benchmarking classificationmodels for software defect prediction: A proposed framework and novelfindings,” IEEE Transactions on Software Engineering, vol. 34, no. 4, pp.485–496, 2008.
-
網(wǎng)絡(luò)安全
+關(guān)注
關(guān)注
11文章
3295瀏覽量
61100 -
V2X
+關(guān)注
關(guān)注
25文章
215瀏覽量
44047
原文標(biāo)題:網(wǎng)聯(lián)車輛網(wǎng)絡(luò)安全異常檢測(cè)綜述 | 智車科技
文章出處:【微信號(hào):IV_Technology,微信公眾號(hào):智車科技】歡迎添加關(guān)注!文章轉(zhuǎn)載請(qǐng)注明出處。
發(fā)布評(píng)論請(qǐng)先 登錄
專家解讀 | NIST網(wǎng)絡(luò)安全框架(1):框架概覽
網(wǎng)絡(luò)安全隱患的分析
2020 年網(wǎng)絡(luò)安全的四大變化
為什么網(wǎng)絡(luò)攻擊無(wú)法與自動(dòng)駕駛相匹敵
定位技術(shù)在網(wǎng)絡(luò)安全領(lǐng)域中的應(yīng)用是什么
網(wǎng)絡(luò)安全類學(xué)習(xí)資源相關(guān)資料推薦
網(wǎng)絡(luò)安全技術(shù)課件,網(wǎng)絡(luò)安全技術(shù)精品課程
網(wǎng)絡(luò)安全檢測(cè)與監(jiān)控技術(shù)的研究
探討2019年的網(wǎng)絡(luò)安全重要趨勢(shì)
入侵檢測(cè)技術(shù)在網(wǎng)絡(luò)安全中有什么樣的應(yīng)用



 探討異常檢測(cè)技術(shù)在網(wǎng)聯(lián)車輛網(wǎng)絡(luò)安全
探討異常檢測(cè)技術(shù)在網(wǎng)聯(lián)車輛網(wǎng)絡(luò)安全








評(píng)論